Motivation
GSM telephony is the world’s most popular communication technology spanning most countries and connecting over four billion devices. The security standards for voice and text messaging date back to 1990 and have never been overhauled. Our GSM Security Project creates tools to test and document vulnerabilities in GSM networks around the world so to ignite the discussion over whether GSM calls can and should be secured. The project is summarized in this Black Hat 2010 presentation.
Recording calls
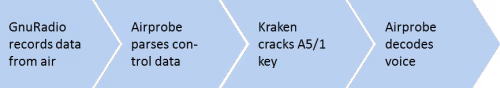
GSM data can be recorded off the air using, for example, a programmable radio such as the USRP. GnuRadio provides the tools to record channels while Airprobe’s gsm-receiver decodes the control traffic and—in scenarios where no encryption is used or where the encryption key is known—also decodes voice traffic.
Cracking A5/1
When GSM uses A5/1 encryption, the secret key can be extracted from recorded traffic. Given two encrypted known plaintext messages, the Kraken utility that runs on a PC finds the secret key with around 90% probability within seconds in a set of rainbow tables. Our current table set took 2 months to compute and contains 40 tables for a total of 2TB. Further details on cracking A5/1 using rainbow tables are provided in this white paper: Attacking Phone Privacy.
Defenses
Short term protocol patches already exists that make cracking much harder by not disclosing known plaintext unnecessarily (3GPP TS44.006, Section 5.2). These patched should be deployed with high priority. In the long term, GSM (2G) will not provide sufficient security and stronger alternatives such as UMTS (3G) and LTE (4G) should be preferred.
Tools
The following tools are used to analyze voice calls:
- GnuRadio is included in recent Linux distributions Recording data requires a programmable radio receiver such as the USRP
- Airprobe is available here
- Background on Kraken’s rainbow tables are provided on the project web page
- Kraken uses rainbow tables that are available through Bittorrent.
Please use these tools carefully and never intentionally record other people’s conversations. We do encourage you to use them to test the security of your cell phone service and discuss your results on the project mailing list.